EDITOR’S NOTE (March 12, 2026): This blog was originally written in January 2020 but the content remains informative and relevant today. It was also revised on March 4, 2022. Some of the original content has been updated based on the most recent current events.
International political relationships sometimes increase the risk of cyber‑attacks. In light of recent events, many organizations are now closely monitoring Iran‑linked APT activity. Even if a particular wave of activity does not directly affect your environment, threats from new and existing Iran‑aligned groups will continue to emerge and evolve — and a well‑designed threat intelligence program helps you understand which actors pose the most likely and impactful risk so you can prioritize defenses and testing.
Many of our clients use VECTR not only as a purple team management tool but also to operationalize CTI against defense success metrics. When an organization records purple team results inside VECTR, they have a fast, repeatable way to see where gaps exist and what to tackle next.
When a threat intel program focuses on known actors, it typically starts by enumerating the groups to consider. Below is a sample set of Iran‑linked APT groups (aligned to VECTR naming) that we commonly ingest into assessments. For each group we list common aliases, the reported affiliation, a short summary of activity, and vendor reporting citations:
MuddyWater
- Aliases: Seedworm; Static Kitten; TEMP.Zagros
- Reported affiliation: Ministry of Intelligence and Security (MOIS)
- Summary: Spear‑phishing, credential theft, custom malware (GhostFetch); global targeting
- References: Thrive Cyber Report (Mar 3, 2026); GBHackers (Mar 4, 2026); Security.com (Mar 5, 2026)
APT33
- Aliases: Elfin; Refined Kitten; Magnallium
- Reported affiliation: Islamic Revolutionary Guard Corps (IRGC)
- Summary: Espionage, supply‑chain attacks, password spraying; targets include aerospace, energy, and government sectors
- References: Picus Security (Mar 6, 2026); GBHackers (Mar 4, 2026)
OilRig
- Aliases: COBALT GYPSY; IRN2; APT34; Helix Kitten; Evasive Serpens; Hazel Sandstorm; EUROPIUM; ITG13; Earth Simnavaz; Crambus; TA452
- Reported affiliation: Ministry of Intelligence and Security (MOIS)
- Summary: Phishing, credential harvesting, web‑shell deployment; espionage mainly against energy and telecom sectors
- References: Thrive Cyber Report (Mar 3, 2026); GBHackers (Mar 4, 2026)
Magic Hound
- Aliases: TA453; COBALT ILLUSION; Charming Kitten; ITG18; Phosphorus; Newscaster; APT35; Mint Sandstorm
- Reported affiliation: Islamic Revolutionary Guard Corps (IRGC)
- Summary: Spear‑phishing and credential harvesting targeting political, military, and commercial entities
- References: HSToday (Mar 1, 2026)
APT42
- Aliases: Charming Kitten / Phosphorus; TA453; Yellow Garuda; ITG18
- Reported affiliation: Islamic Revolutionary Guard Corps (IRGC)
- Summary: Cyber‑espionage against dissidents, academics, and strategic sectors
- References: HawkEye Threat Advisory (Mar 6, 2026)
Agrius
- Aliases: Pink Sandstorm; AMERICIUM; Agonizing Serpens; BlackShadow
- Reported affiliation: IRGC‑linked
- Summary: Performs destructive operations, including wiper malware
- References: Thrive Cyber Report (Mar 3, 2026)
CURIUM
- Aliases: Crimson Sandstorm; TA456; Tortoise Shell; Yellow Liderc
- Reported affiliation: Iran‑aligned
- Summary: Targeting defense and telecom sectors with espionage and disruptive operations
- References: GBHackers (Mar 4, 2026)
Cyber Av3ngers
- Aliases: Soldiers of Solomon
- Reported affiliation: Islamic Revolutionary Guard Corps (IRGC)
- Summary: ICS/OT disruption; often poses as hacktivists
- References: CSIS (Jan 14, 2026); HawkEye Threat Advisory (Mar 6, 2026)
Void Manticore
- Aliases: Storm‑842; Handala
- Reported affiliation: Iranian destructive operations units
- Summary: Wiper attacks and hack‑and‑leak campaigns
- References: HawkEye Threat Advisory (Mar 6, 2026)
Cotton Sandstorm
- Aliases: Emennet Pasargad; Haywire Kitten; MarnanBridge
- Reported affiliation: Islamic Revolutionary Guard Corps (IRGC)
- Summary: Influence operations, DDoS, account hijacking, data theft, hack‑and‑leak
- References: Check Point Research (Mar 1, 2026); The Register (Mar 2, 2026)
Altoufan Team
- Aliases: Cyber persona for Cotton Sandworm
- Reported affiliation: IRGC‑aligned persona
- Summary: Recently claimed disruptive attacks in Bahrain and the Gulf region
- References: The Register (Mar 2, 2026)
DieNet
- Aliases: (none listed)
- Reported affiliation: Pro‑Iran, likely state‑directed
- Summary: DDoS and infrastructure attacks against airports, banks, energy; active in the Gulf region
- References: HawkEye Threat Advisory (Mar 6, 2026); DSCI Advisory (Feb 2026)
*Note on attribution: the reported affiliations above are vendor‑ or government‑attributed and can vary across sources — treat them as analyst attributions rather than incontrovertible fact. Use multiple sources and your organization’s risk model when deciding which groups to prioritize.
Using this CTI in VECTR
At the time of the original posting, APT33 was highly active, and was used as an example for the following process using VECTR™.
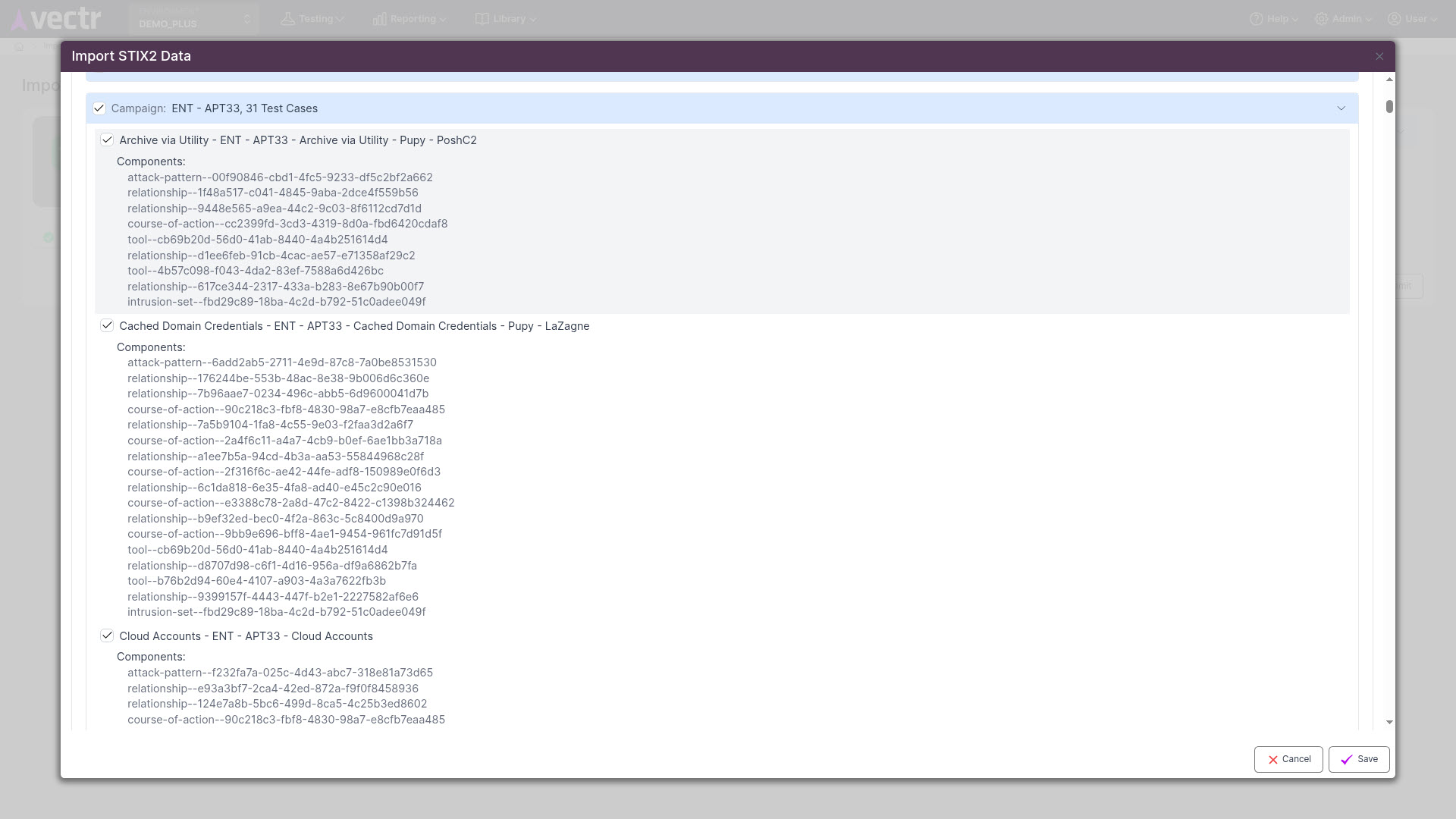
MITRE ATT&CK remains a primary source for technique‑level mapping, and MITRE’s CTI (STIX 2.0) is available on GitHub for direct consumption by platforms like VECTR. When you import threat actor CTI into VECTR and combine it with your purple team test results, you can immediately see how existing coverage maps to the techniques and procedures attributed to selected Iran‑linked groups (or across the whole ATT&CK matrix).
Sample workflow (in VECTR):
- In Administration, import Enterprise ATT&CK (Full) or drop STIX 2.0 CTI bundles for the groups you care about.
- Select the specific Iran‑linked APT groups you want to include in the assessment.
- Filter or map your existing test cases to the imported techniques (if needed).
- Create a dedicated campaign that contains the techniques observed for those actor groups.
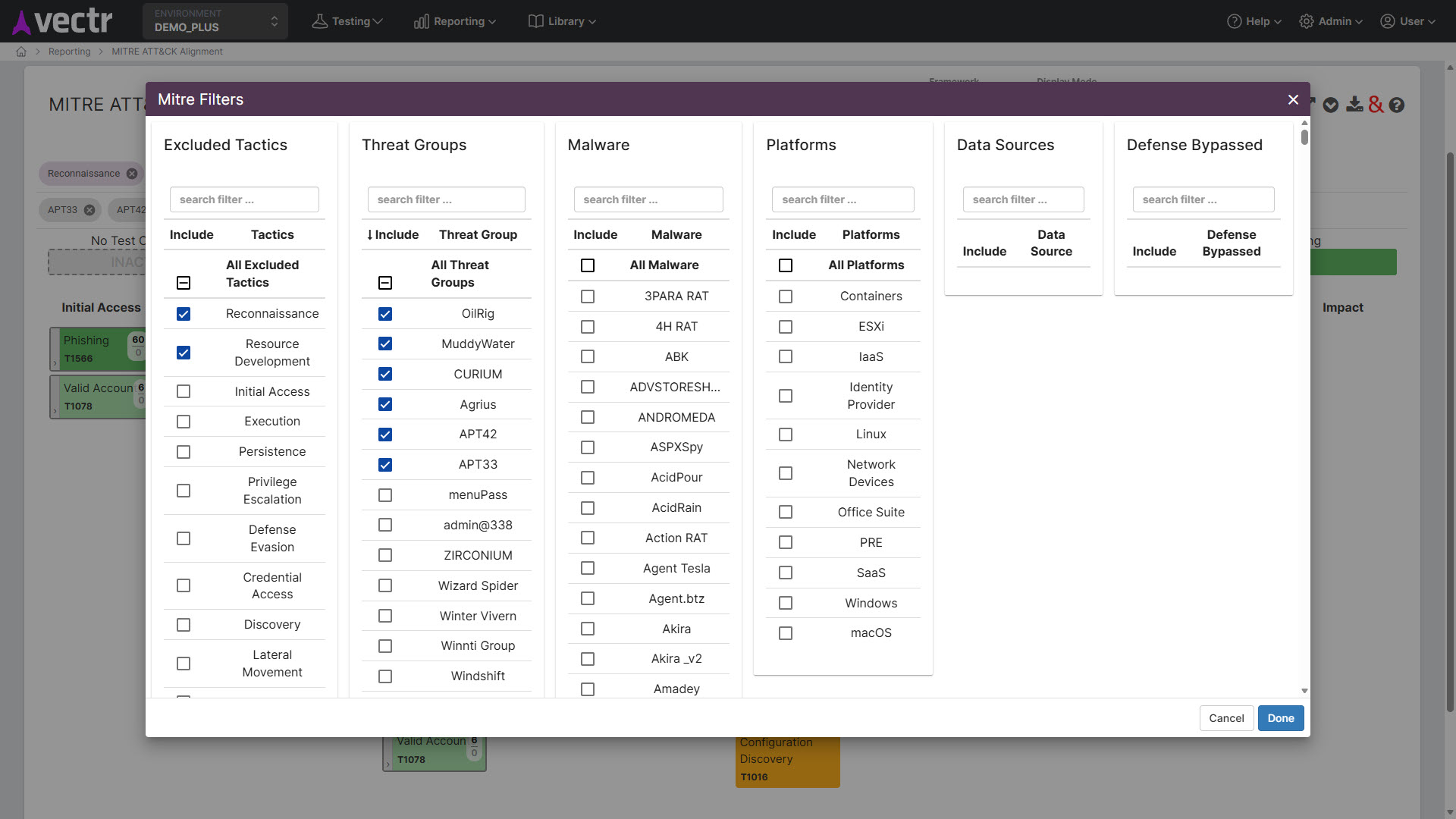
Sample dataset showing MITRE ATT&CK™ Heatmap Report filtering on one or more APT’s
Once filtering is complete, VECTR’s ATT&CK heatmap shows the techniques attributed to the selected groups, color‑coded by the most recent assessment status of your mapped purple team test cases. Red/orange/yellow cells indicate techniques where the actors tend to operate and where your defenses need more work. Grey cells show techniques not yet covered by your tests — a clear prioritized backlog for future assessments.

Why this matters
By blending threat actor CTI with repeatable purple team results, you gain both tactical and strategic advantages:
- Tactical: Prioritize mitigations and detection engineering for techniques exploited by actors assessed to be most relevant to your environment.
- Operational: Turn heatmap gaps into focused purple team campaigns, detection rules, and automated telemetry checks.
- Strategic: Communicate risk and readiness to leadership with objective, technique‑level coverage metrics tied to named actor activity.
Getting Started
If you’re not already running purple teams in VECTR but want to model Iran‑linked threat actor tactics, it’s straightforward to begin. VECTR™ supports drag‑and‑drop STIX 2.0 ingestion from ATT&CK and lets you use CTI to plan assessments and threat emulations. In an upcoming release we will open a public TAXII server to enable community‑driven sharing and enrichment of CTI, including assessment plans and detection content.
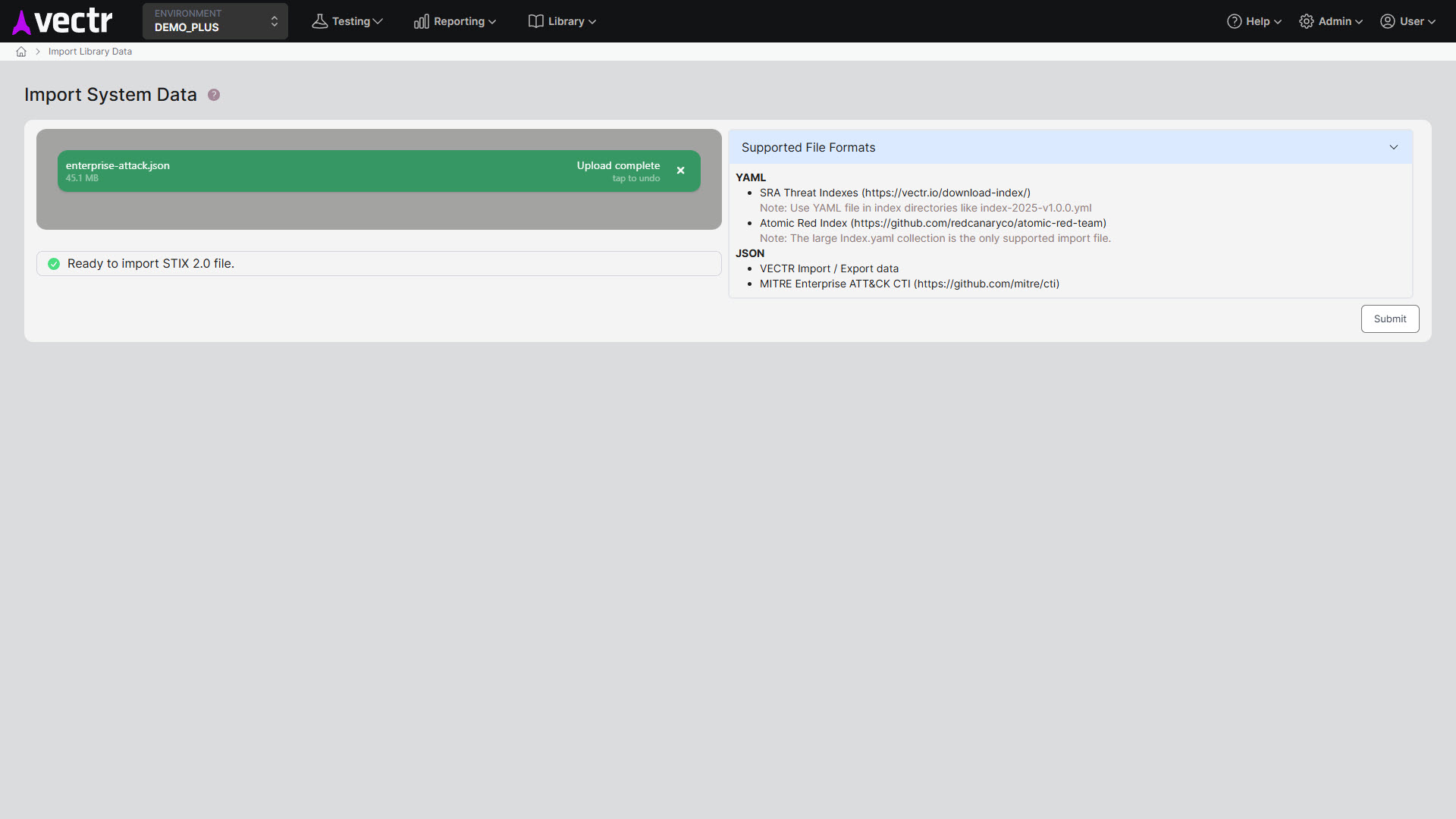
In Administration, import from Enterprise ATT&CK (Full)
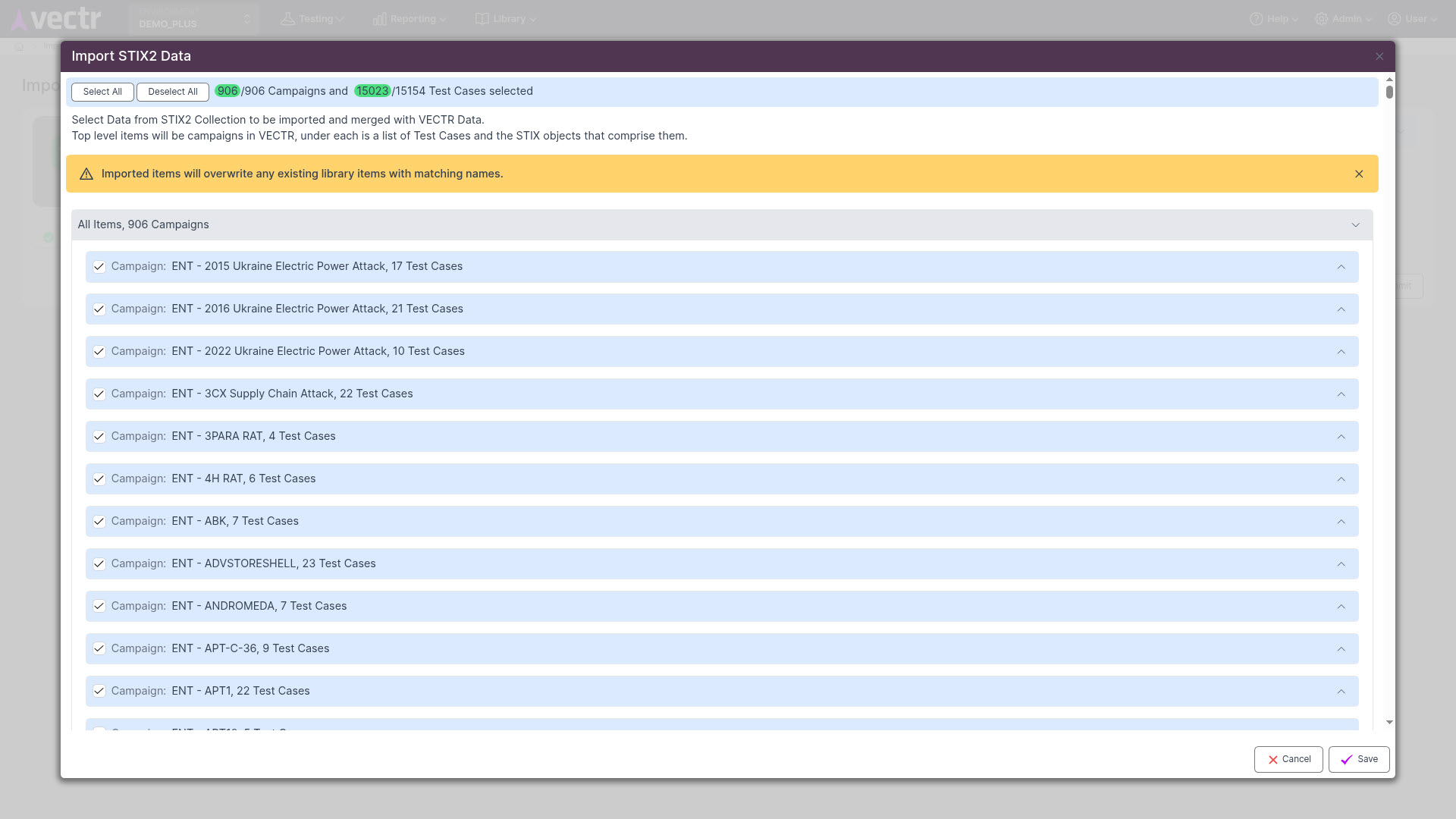
Select the specific APT groups you’d like to bring in
Filter test cases if desired
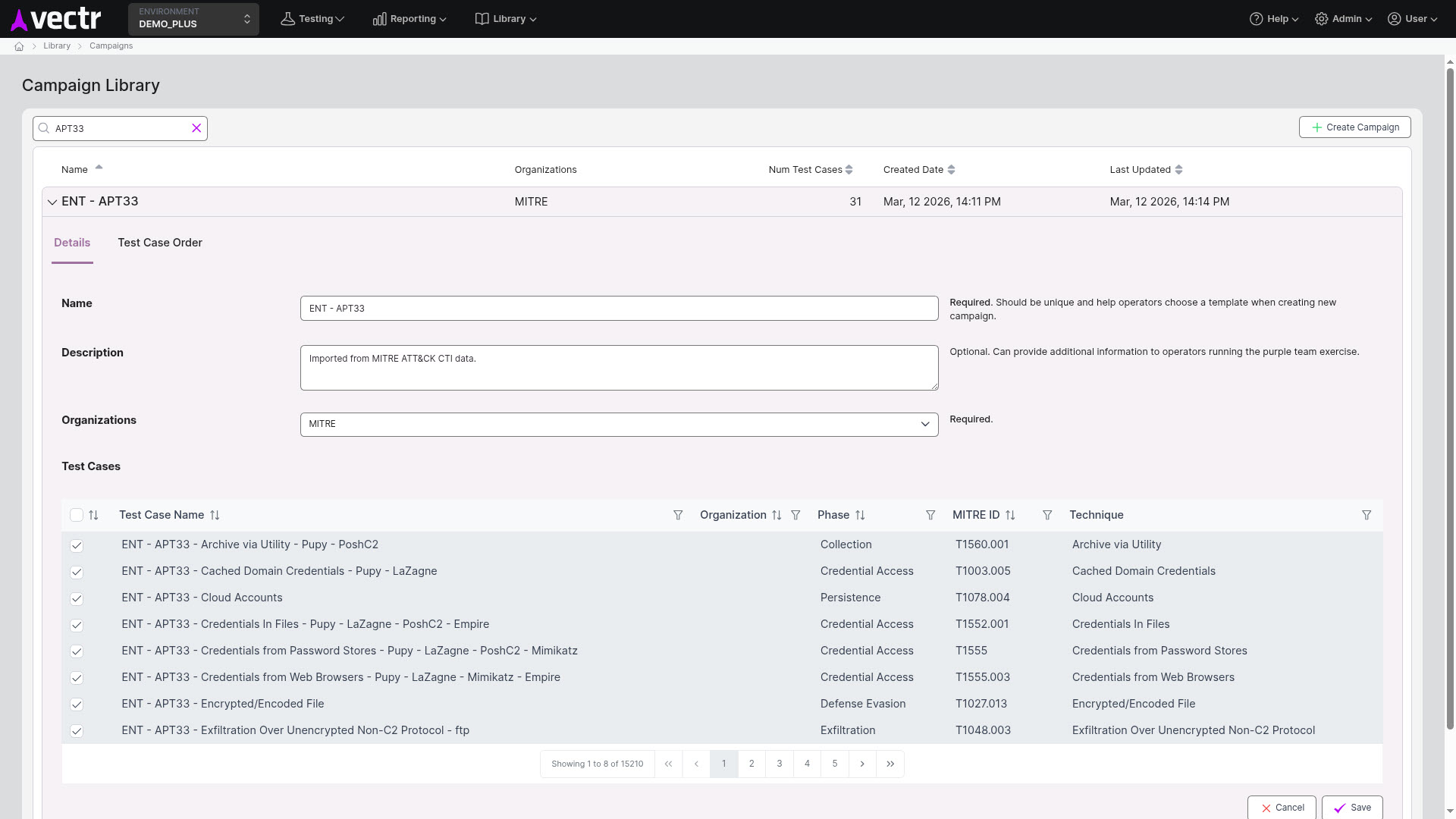
Create a dedicated campaign based on these threat actor groups’ techniques
Get VECTR
You can use VECTR entirely for free — download the Community version at https://vectr.io/vectr-community and join the VECTR Squadron mailing list at vectr.io to stay informed about new releases and features.
If you’d like help mapping vendor reporting to MITRE groups, building campaigns for any of the Iran‑linked groups above, or operationalizing the results in your SOC, reach out and we can assist with tailored guidance and runbooks.
Mike Pinch
Mike is Security Risk Advisors’ Chief Technology Officer, heading innovation, software development, AI research & development and architecture for SRA’s platforms. Mike is a thought leader in security data lake-centric capabilities design. He develops in Azure and AWS, and in emerging use cases and tools surrounding LLMs. Mike is certified across cloud platforms and is a Microsoft MVP in AI Security.
Prior to joining Security Risk Advisors in 2018, Mike served as the CISO at the University of Rochester Medical Center. Mike is nationally recognized as a leader in the field of cybersecurity, has spoken at conferences including HITRUST, H-ISAC, RSS, and has contributed to national standards for health care cybersecurity frameworks.





