Recently at the SANS Tactical Detection and Data Analytics conference, Nick Ascoli and Kevin Foster introduced the open source Threat Alert Logic Repository (“TALR”). TALR is intended to automate detection through the sharing of SIEM rules.
One of the most frequent questions we get when discussing new attacks, or performing purple teams is “how do other organizations detect this?” Lots of organizations share Indicators of Compromise (IOCs) such as IP addresses, hashes, etc., but few share their SIEM detections, which focus on attacker behavior. This makes it hard for organizations to answer questions like:
- Would deploying a new tool give us additional visibility?
- How do we compare to our peers from a detection standpoint?
- We’ve got a rule for this – but is it the best rule we could have?
Another common problem is an inability to keep pace with the offensive community. Reading every tweet posted by the offensive security community can be a full-time job, and only a subset of offensive researchers releases guidelines on detecting their latest and greatest techniques. Even when a researcher is thorough enough to post detection guidelines, often they’re just that – guidelines. You may get a Plug and Play PoC and some abstract thoughts on how you might be able to detect the attack in your environment. The onus of implementing a detection is placed squarely on the defender (there’s a good reason for that), while attackers often just get to copy and paste.
The hardest part about designing robust detections is that every environment is different. There are lots of different SIEM vendors on the market, each one with their own query syntax. The offensive community releases detection guidelines because they can’t make assumptions about the logging ability and query syntax of every SIEM in every environment, it’s just not practical.
Enter TALR
Most organizations have two primary sources of detection rules, the ones that come out of the box with the SIEM (or other toolset), and the ones written in house by their analysts. The goal of TALR is to provide a third source of detection rules, allowing organizations to more easily keep pace with what attackers are doing through community sharing and automation.
TALR is an open source repository of detection logic, written in a vendor-agnostic format which can be translated for ingestion in to different SIEM’s. TALR rules are written in Sigma format (a YAML format designed to represent SIEM rules), and intended to be stored and transmitted as STIX objects by a TAXII server. SRA has written a proof-of-concept script, stix2sigmac, which allows for community vetted detection rules to be automatically ingested by supported SIEMs.
TALR / stix2sigmac has several potential benefits:
- Faster alerting through automated rule ingestion in to your SIEM
- Benchmarks to compare your existing ruleset against rules written by other organizations
- Increased community sharing of detection rules – moving past brittle IOC’s to more reliable behavioral based indicators
- Better situational awareness by linking MITRE ATT&CK techniques, threat intelligence, and TALR detection logic together
TALR Automation

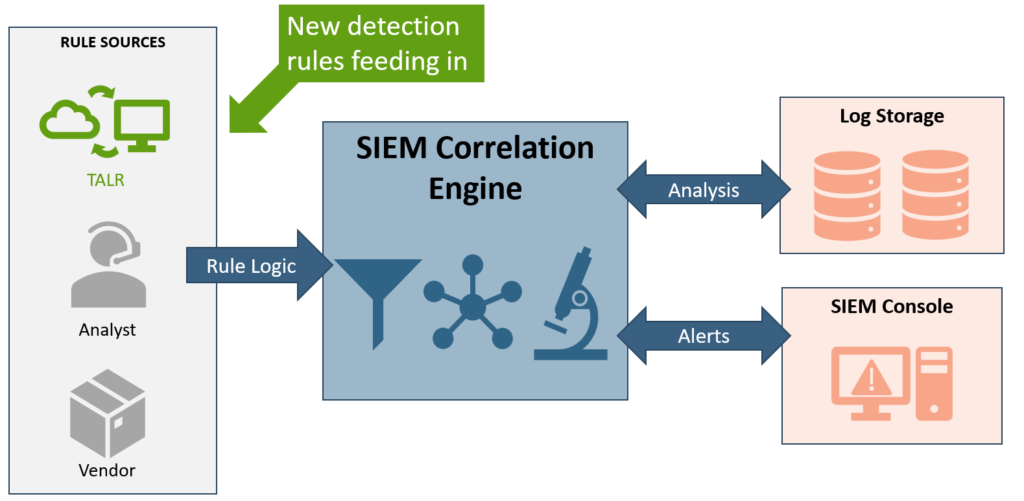
Figure 2: The workflow above shows the automated ingestion of new detection rules from several TAXII servers to a SIEMs correlation engine
In the diagram above, we’ve documented a theoretical workflow using TALR and stix2sigmac. Moving from left to right, TALR rules can be stored on a TAXII server as STIX Objects for distribution. A benefit of using TAXII is that it’s an open-source platform, and anyone can stand up their own TAXII server. In this example, we have three TAXII servers maintained by different sources providing rules for our SIEM infrastructure. After a bundle of TALR rules has been retrieved from a TAXII server, stix2sigmac can be used to convert the vendor-agnostic rules in to a format which is consumable by several popular SIEM platforms. The rule conversion is done through Sigmac, which is associated with the core Sigma project. Currently, converted Sigma rules can be manually copied and pasted in to a SIEM – or for select platforms automatically inserted via the SIEMs API.
As new rules are published to a TAXII server, they can be automatically downloaded and ingested in to a SIEM by running a download query in conjunction with the stix2sigmac script as a cron job. As new detections are created and uploaded to the TAXII server, organizations who are subscribed to the TAXII server can benefit from those detections – without requiring a FTE to monitor Twitter.
Increased Situational Awareness
TALR rules are initially written in a modified Sigma format, which has been extended with some new fields to allow for version tracking and additional meta-data required by STIX / TAXII. After a rule has been initially written in Sigma, the rule needs to be converted to a JSON formatted STIX Domain Object (“SDO”) so that it can be uploaded to a TAXII server. STIX also allows for the creation of STIX Relationship Objects (“SRO”), which can be used to link various SDO’s together, allowing for the documentation of relationships between SDO’s.
By storing a detection rule as an SDO and relating it back to the Object it was designed to detect with an SRO, we can link TALR’s detection logic to traditional threat intelligence. When this rule fires in an environment, additional queries to a TAXII server can provide any other Objects linked to the rule with an SRO.
Put simply, the reason we chose TAXII as our distribution mechanism is because we can create relationships between TALR rules and MITRE ATT&CK, pentest blogs, tweets, IOC’s, and anything else a SIEM analyst might find helpful when deciding how to action a new alert.
TALR Roadmap:
By Q2 2019, our aim is to have a public TAXII server hosting the TALR rules as STIX objects for community use and contribution. In the interim – we will continue to add rules to the public repository, integrate any new open source rule sources, and welcome public contribution of rules.
Links:
TALR: https://github.com/SecurityRiskAdvisors/TALR
Sigma: https://github.com/Neo23x0/sigma
Conference Slides: https://www.sans.org/cyber-security-summit/archives/file/summit-archive-1544034674.pdf