Overview
At SRA, we have seen firsthand that incorporating both penetration tests and purple teams in a cyber security program provides a healthy balance between increasing both prevention and detection capabilities. A penetration test is a simulated cyber-attack against a specific network to highlight vulnerabilities and test prevention capabilities. Performing penetration tests against your corporate, cloud, and OT infrastructure from different vantage points is a critical component of a sound cyber security program. Let’s look at some of these penetration test assessments, SRA’s unique methodology/toolsets, and some client stories that demonstrate how SRA tailors pen test offerings for our clients.
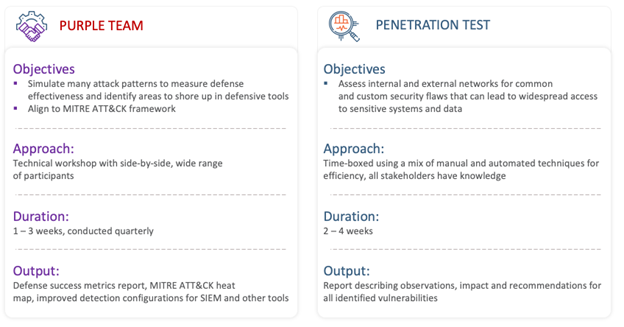
Purple Team vs. Penetration Test Comparison
External Penetration Test
An external penetration test is used to identify insecure applications, cloud services, network services, remote access, overly permissive access rules, and other configuration settings that could allow an Internet-based attacker to compromise systems, applications, and data. This is the most common penetration test that we see clients request, which should come as no surprise, since Internet-facing systems present one of the biggest risks to an enterprise. The duration of these assessments can be anywhere from 1 week to 6 weeks, depending on the size of the organization.
While these objectives sound great, your results can vary drastically between different penetration testing teams. We have seen this time and time again. There are many factors that play a role in the outcome of an external penetration test such as Internet “footprinting” capabilities, team methodologies, TTPs, and time.
Footprinting, the process of performing reconnaissance to identify Internet-facing domains, IP addresses, and network blocks, is a critical first step in this assessment and one that SRA places a heavy emphasis on. For an in-depth look at one of the ways we identify network blocks owned by an organization, give this two-part series on SHADOWSTAR by Peter Crampton a read. In addition to this custom process and tooling, SRA has streamlined our footprinting process and routinely identify assets on the Internet that our clients didn’t realize were there. Having this accurate and complete representation of our client’s Internet-facing systems prepares us for providing more complete coverage during testing.
With the shift to cloud and a constantly changing technology stack, we are seeing an increase in services and new application deployments in popular cloud platforms including AWS, Azure, and GCP. This has often times left sensitive services and data exposed through S3 Buckets, Azure Blob Storage Containers, and hosted databases. Thorough footprinting and reconnaissance is necessary to compile a comprehensive list of these types of cloud assets for further exploitation.
Searching for secrets (e.g., credentials, access tokens), a key part of the open-source intelligence (OSINT) gathering phase, is another step in this assessment that SRA has devoted significant research to. While many tools exist in the open-source community for identifying secrets in public repositories (e.g., GitHub), it can be a tedious task to identify and sift through repositories and commit history. To help automate this process, SRA developed SIFTR™, which scans public repositories to identify sensitive information such as usernames and passwords, encryption keys, internal system information, and more. Many of our clients use this as a continuous service (which also includes monitoring data breaches), however, this is also used during external penetration tests to assist with secret searching.
From compromised domain credentials to web shells, and business logic flaws to internal network access, SRA has performed extensive external testing across various industries. Our manual testing methodology is only complimented with automated tools as a “cleanup” activity and is not the baseline for our assessments. By making sure to stay on top of the latest shifts in technology, and not just the techniques/vulnerabilities, SRA provides coverage across the entire external perimeter instead of just a vulnerability scan.
External Penetration Test – Client Success Story
Challenge
- A large financial institution needed to understand the risk surface of their Internet-facing systems to a malicious actor on a quarterly basis. They also wanted to identify vulnerable systems as they were exposed to the Internet.
Solution
- Executed a 6 week-long external network penetration test each quarter.
- Identified new domains and services across their footprint each week.
Benefit
- Exploited an attack chain to demonstrate how a malicious actor could compromise domain credentials, bypass VPN endpoint checks, and bypass multi-factor authentication (MFA) controls through “push-bombing”, to access the internal network.
- Located sensitive information on a GitHub repository using targeted searches against the historical codebase.
- Identified high-risk vulnerabilities including exposed database credentials, default credentials on web applications, and exposed development microservices.
Internal Penetration Test
An internal penetration test is used to identify system and network service vulnerabilities, insecure configurations, etc. This assesses whether a motivated insider, visitor, or attacker with internal network access, could elevate privileges to steal data for profit, or gain access to protected systems and data in your offices and data centers. Including this exercise in your security program is just as crucial because as we all know, it’s not a question of “if”, but rather “when”, the external perimeter gets breached. Internal networks typically contain a significant number of systems compared to the external network, which opens more areas of opportunity for an attacker.
While some penetration testing teams have the goal of compromising a Domain Admin account and calling it a day, this is only the beginning in our methodology. Many of the same vulnerabilities and insecure configurations are common across different enterprises, but these exercises are not a one-size-fits-all. From a blind perspective and only access to a network port, our goal is to:
- Identify all the different avenues we can take to obtain privileged access, while documenting the vulnerabilities/misconfigurations that allowed us to get there.
- Demonstrate control of IT infrastructure (e.g., Active Directory, virtualization environment).
- Access any unique “crown-jewels” of the business such as Payment Card Industry (PCI) data or a secret server.
- Access personally identifiable information (PII) or protected health information (PHI).
With the recent pandemic halting travel and requiring these exercises to be done remotely, it should be noted that returning to on-site execution at a physical office will provide the best value for reasons such as the ability to include:
- Proximity-based attacks (e.g., mouse-jacking)
- Physical-based attacks (e.g., USB attacks)
- Network-port hopping
- Face-to-face and real-time communication
SRA has performed pen tests against a wide variety of unique industries and network architectures (e.g., fully cloud based with MacOS endpoints), which has presented distinct challenges. Our Research & Innovation team has developed custom toolsets to overcome some of these challenges. SRA has also invested a significant amount of time into hefty password-cracking rigs with extensive capabilities that are required during the modern age of hardened password policies.
Often combined with an internal assessment is a wireless penetration test, which identifies misconfigurations in enterprise and guest wireless networks that can allow for access to a network or the capturing of user credentials. While not typically as high on the priority list, testing the security of wireless networks is just as important within enterprise security to provide a defense-in-depth approach. Development in wireless security has certainly advanced, but SRA continues to see misconfigurations and insecure configurations that allow for these networks to get compromised. By combining warwalking techniques with modern toolsets, we document visible networks, confirm known networks, and create an attack plan based on the type of wireless security in use.
Internal Penetration Test – Client Success Story
Challenge
- A global entertainment company needed to understand the risk surface of their commercial ships to both network level and physical access attacks
Solution
- Boarded a newly built ship as passengers to execute a multi-day network and physical penetration test.
- Simulated attack paths as a malicious customer and as an insider threat while on-board.
Benefit
- Documented gaps in corporate network controls and access management that allowed for unauthorized and potentially dangerous access to ship systems.
- Exploited several system controls to demonstrate how an attacker can access customer-owned PCI data, obtain control of the ship, and access the onshore corporate network from sea.
- Agency began implementing new, secure controls to address observations after we provided a demonstration to highlight potential damages incurred by the identified attack paths.
Web Application Penetration Test
A web application penetration test identifies insecure web server software, application functionality, and configuration settings that are susceptible to both common and custom attacks. These attacks could result in data compromise, elevated privilege or administrative application control, or reputation damage. The duration of these assessments can be anywhere from 1 week to several weeks, depending on the complexity and number of applications being tested.
Web applications are typically the face of a business with many moving parts. Securing these applications, especially older ones, can be a difficult and tedious process. Many corporate applications may only go through an automated web application scan before getting pushed to production on the Internet! However, modern, single-page application frameworks (e.g., AngularJS, ReactJS), have made automated testing more complex. With network-based vulnerabilities producing diminishing returns for attackers, web applications have been a prime target for many years and will continue to be. It’s important to give pre-production and core applications the dedicated testing they deserve.
While web applications are certainly tested during an external penetration test, time constraints and a lack of credentials only allow for limited testing on areas that appear most weak or sensitive. On a web application penetration test, we perform testing of applications from the perspectives of both an unauthenticated and authenticated attacker and cover the OWASP Top 10. For complex and/or unique applications, developers can provide walkthroughs, source code, and diagrams that assist SRA in understanding the components and architecture on the backend. This allows for the most comprehensive assessment against an application, as opposed to blind testing.
Web Application Penetration Test – Client Success Story
Challenge
- A large telecommunications organization wanted to continually understand the risk surface exposed by the extensive array of products, services, and technologies that are regularly integrated into the organization.
Solution
- Performed continuous web application penetration tests for several years against existing and newly developed applications.
- Collaborated closely with the client’s incident response team to tackle critical security vulnerabilities that posed an immediate risk to the network.
Benefit
- Executed an attack chain to illustrate how an attacker could exploit misconfigured microservices to extract customer data.
- Discovered critical vulnerabilities such as multi-factor authentication bypass, business logic flaws, and injection-based vulnerabilities (e.g., Log4Shell) on publicly available services.
- Improved the internal security team’s understanding of specialized security assessments such as mobile and hardware-based assessments.
OT (Operational Technology) and Cyber Physical Systems (CPS) Penetration Test
What is OT and CPS, you ask? That can be answered quite perfectly by our own Jason Rivera right here. This assessment is far from your classic penetration test and is much more collaborative in nature because of the separation of IT/OT, the sensitivity of these systems, and the critical foundation that they provide for an organization. An OT penetration test typically lasts 2-3 weeks and simulates the risk of a malicious actor who has gained access to one (1) or more network zones within the Purdue Model.
We identify OT/ICS assets, protocols, misconfigurations, known vulnerabilities, and connectivity that could be exploited to impact site operations. More importantly, we use safe, light-touch, targeted, and highly coordinated testing to minimize risk to site operations and operator safety. Combining this assessment within an OT program (e.g., inventory management using SBOMs) is critical within an industry that is trying to catch up to modern-day cybersecurity standards.
OT Penetration Test – Client Success Story
Challenge
- A large energy sector organization wanted to understand the risk surface exposed to a malicious actor who has access to the OT network, as well as determine if segmentation controls in place effectively prevent the ability to move from the enterprise network to the industrial control systems (ICS) environment.
Solution
- Executed a week-long OT penetration test and targeted segmentation assessment.
Benefit
- Uncovered several unintended vectors to obtain access to the SCADA/ICS environment from the enterprise network, allowing access to sensitive systems and applications.
- Identified several devices in the OT network with default credentials or no authentication, unauthenticated industrial protocols, and end-of-life systems/software.
- Client was able to prioritize remediation efforts to further secure both the internal and ICS networks.
Conclusion
Choosing the right assessments for an enterprise depends on many factors such as network architecture, Internet footprint, industry risk, etc. Not every type of penetration test will make sense in every environment, but having the right team to perform them is crucial. Our SRA Advisory Red team holds highly accredited certifications such as Offensive Security Certified Professional (OSCP), Offensive Security Certified Expert (OSCE), and Certified Red Team Operator (CRTO). Having a trusted security partner to help identify where to focus efforts and/or perform a continuous testing program with you, can help tremendously in the quest to achieve superior defensive cyber security controls.
Jason Sarnoff
Jason focuses on penetration testing, web application security, purple teams, social engineering/phishing, and wireless security. Jason has worked with clients across several industries including insurance, healthcare, financial, retail, entertainment, and construction.
His role in a project is to lead/execute technical testing and to work with technical teams and leadership in understanding the scope and outcome of a project.
Jason is also CISSP and OSCP certified.





