Introduction
Operational Technology (OT) is a broad term that can be interpreted differently depending on the organization and its business alignment. Defining what “OT” means to your organization is crucial, including identifying and classifying your OT assets. In a recent survey at an ISAC conference, it was found that many organizations do not have a clear list of device types that they consider as their OT.
Why it Matters
Understanding what we’re securing is the first step towards reducing security risk in OT systems and environments. The classification of an asset as OT, IoT, IIoT, IoMT, or traditional IT is not just about terminology but also about understanding its function, connectivity, performance needs, support requirements, and potential impact if it malfunctions or becomes unavailable. Questions to answer as an organization would be:
- What function or process does it perform?
- What connectivity does it require?
- What performance needs does the system have?
- Does it make something or just do something?
- Is it an autonomous, manual, or hybrid system?
- What kind of systems and people need to support it?
- What type of data inputs and outputs are required and what dependencies are required?
- Does it support a critical process or serve a regulatory function?
- What would happen if it wasn’t available or malfunctioned? Can it jeopardize personal safety? Financial or reputational damage?
- Who knows it’s here? Can it be located, seen, touched, communicated with, or maintained?
The Complete Picture
While OT security monitoring and detection products provide asset visibility, that’s (one big) part of the picture. Once visibility is established though, organizations need to know how to respond to potential threats in a way that does not impact critical operations. This includes having an OT Incident Response Plan (IRP), understanding the priority of incidents, and ultimately knowing which assets are your crown jewels.
How to Start
Addressing this question requires collaboration between security, business, site/plant leads, and Engineering and Automation teams. To define the types of assets to consider as OT, you first need to know what systems you have. This could be from a vendor asset management solution or a locally managed Excel file.
Once you have an asset list, you can start to classify your assets as OT based on their role in your organization. This could be as simple as classifying all devices from certain manufacturers as OT, or it could involve a more detailed analysis of how the assets are used in your business.
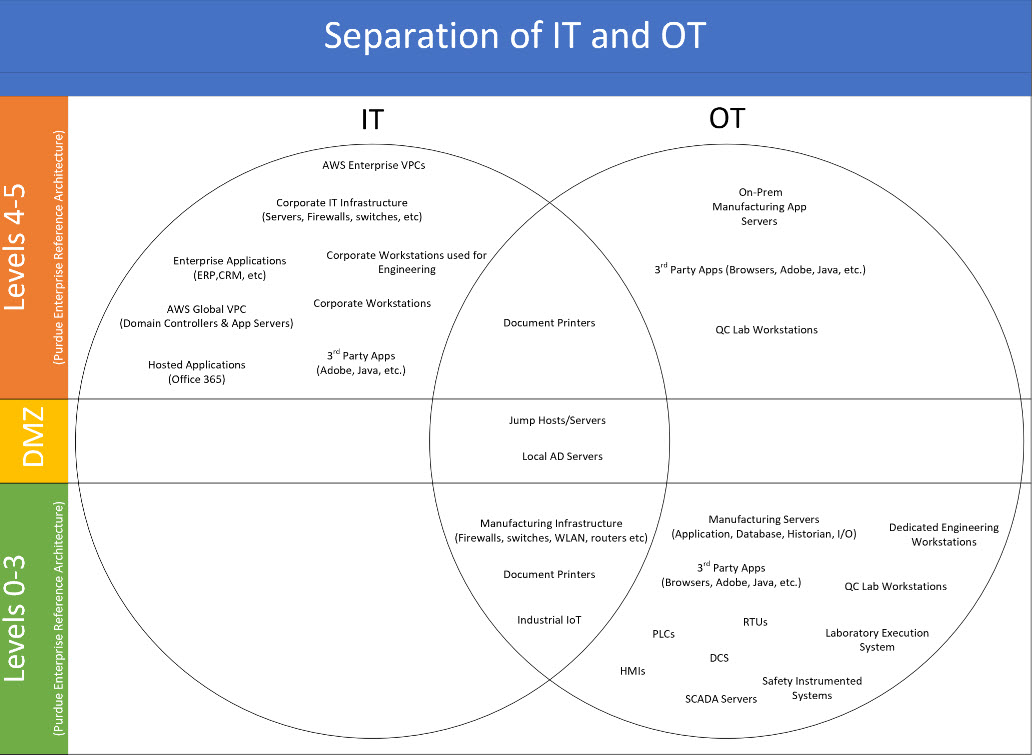 For additional information on the Purdue Enterprise Reference Architecture: https://en.wikipedia.org/wiki/Purdue_Enterprise_Reference_Architecture
For additional information on the Purdue Enterprise Reference Architecture: https://en.wikipedia.org/wiki/Purdue_Enterprise_Reference_Architecture
Here are a few broad stroke efforts to get going:
- Captain Obvious checking in for duty
- Most organizations have device/system naming syntaxes and maybe even include nomenclatures like “-mfg” in the hostname. Start here.
- Framing OT
- You can say that any device directly involved in the physical production of product is OT. That’s the point; this is an organizational decision.
- Keep It Simple
- Since Rockwell, Siemens, Honeywell, and Advantech are all Manufacturing companies (compared to Lenovo, for example) and you’re not trying to solve a philosophical problem, you can simply start with agreeing that their devices in your environment are OT. The IT and Security teams will appreciate this simplicity as a starting point. Once you’ve gained some maturity, you can filter out certain types of their systems, not just considering all OT the same.
Final Thoughts
The ISA/IEC 62443 standards provide comprehensive guidance on OT security and are worth familiarizing yourself with. However, as “Industry 4.0” continues to evolve, the line between “OT and IT” is becoming increasingly blurred. This makes it even more important to have a clear understanding of what assets you consider to be OT, whether they are located on the plant floor or in the cloud.
Remember, it’s better to start simple and gradually increase your understanding of your OT environment. And don’t hesitate to reach out if you need guidance or support.
Jason Rivera
Jason specializes in Cyber Physical Systems (CPS) security strategy program development and controls. He has spoken at H-ISAC, ISACA and multiple CPS security trainings while also serving in OT/IoT security leadership roles since 2018.
He has prior experience with Cybersecurity Operations, Incident Response (IR), Network Security and Risk Management.
In addition to helping clients, Jason has been a go to for SRA in new and emerging services. He has also been a Palo Alto Networks Certified Network Security Administrator (PCNSA) and Cisco Certified Network Associate (CCNA) certified.





