Executive Summary:
As of early 2026, VMware ESXi remains a priority target for both cybercriminals and nation-state actors. Its role as the foundational hypervisor for much of enterprise virtualization makes it a single point of failure, where a compromise can grant an attacker control over hundreds of virtual machines (VMs) simultaneously.
This blog tracks current threat actor activity and offers actionable guidance for defending ESXi environments, including practical hardening measures, detection and threat hunting opportunities based on native ESXi logs, and vendor-recommended security controls.
What is VMware ESXi ?
VMware ESXi is a bare-metal (Type-1) hypervisor that installs directly on physical server hardware without requiring an underlying operating system to create and manage multiple virtual machines (VMs). The virtual machines share the host’s CPU, memory, storage, and network resources. It’s the foundation of VMware’s vSphere virtualization platform and is widely deployed in enterprise data centers, enabling organizations to consolidate dozens of servers, applications, and workloads onto a single physical machine. ESXi is typically managed remotely through vCenter Server or the web-based Host Client rather than through a local console.
Why Threat Actors Target ESXi
- Centralized Control: Access to the hypervisor layer allows threat actors to manage, encrypt, or disable multiple virtual machines from a single control point.
- Visibility Blind Spots: ESXi hosts lack traditional EDR/XDR agents, as these tools often cannot be installed on these devices directly and typically run inside the guest VMs rather than on the bare-metal hypervisor itself. This makes malicious activity harder to detect.
- Persistence: By establishing a backdoor at the hypervisor level (e.g., via BRICKSTORM), attackers can maintain long-term access that survives VM reboots and guest-level reimaging.
- Administrative Design Flaws: Vulnerabilities such as CVE-2024-37085 allow attackers to gain full administrative control simply by joining a domain group named “ESX Admins,” which the hypervisor may automatically trust.
Recent Threat Activity Targeting VMware ESXi
In late 2025 and early 2026, adversaries have actively exploited critical VMware ESXi vulnerabilities, elevating the risk posture for virtualized infrastructure worldwide. Security researchers have documented a complex exploit chain targeting multiple ESXi zero-day vulnerabilities (CVE-2025-22224, CVE-2025-22225, and CVE-2025-22226) that were being used in the wild more than a year before public disclosure and patch release. These flaws allow local authenticated users inside a VM to escape isolation, gain hypervisor-level execution, and compromise the host system while bypassing traditional network defenses and creating a foothold for a broader system compromise. The exploit kits included specialized components like VSOCK-based backdoors and kernel drivers to evade detection and reach the ESXi hypervisor directly.
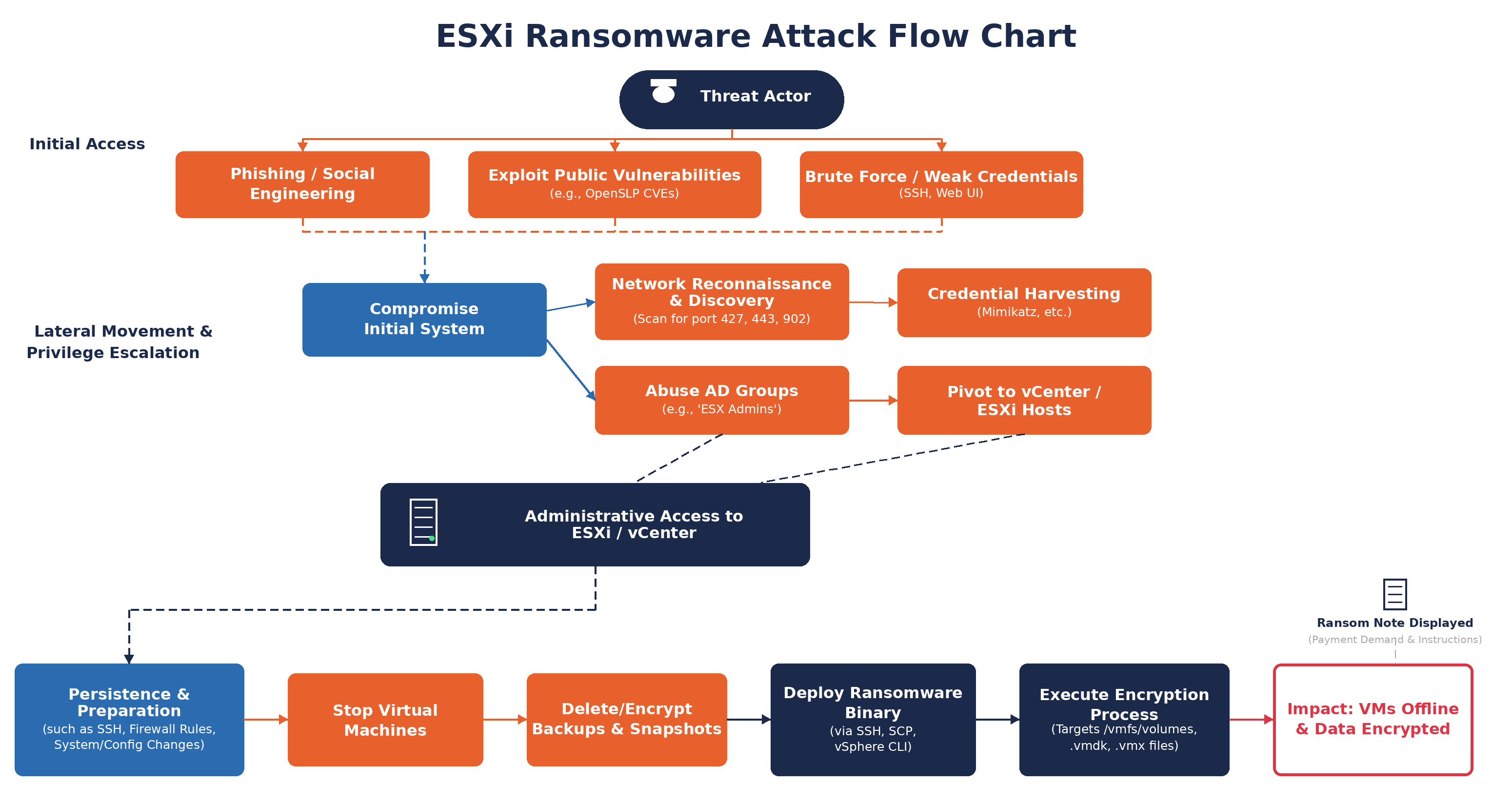
Beyond zero-day exploitation, ransomware groups are increasingly focusing on ESXi environments as high-impact targets. Ransomware operations specifically tailored to VMware hypervisors have grown significantly over recent years, with more attackers viewing ESXi hosts as high-value infrastructure points due to the fact that encrypting an entire fleet of virtual machines at once yields a much larger operational impact than targeting individual endpoints.
Industries such as retail and enterprise IT have already seen campaigns where ransomware actors gained access through compromised credentials or vendor access to escalate and encrypt ESXi hypervisors, causing extended outages and mission-critical disruptions. For example, in April 2025, a massive attack on Marks & Spencer encrypted its ESXi hypervisors, causing over $400 million in damages by halting online sales and logistics. Reporting attributed the intrusion to Scattered Spider in collaboration with Dragonforce ransomware.
Active Ransomware Families & Threat Actors Targeting VMware ESXi and Broader Enterprise Environments
Below is a current snapshot of ransomware groups and threat actors either known to focus on ESXi hosts or are significant in the broader ransomware ecosystem (with relevance to hypervisor risk):
| Threat Actor / Family | Threat Type | ESXi / Hypervisor Relevance |
| LockBit | Ransomware | Highly prolific; newer variants (incl. LockBit 5.0) include dedicated strategies for virtualized infrastructures |
| DragonForce | Ransomware | Observed in ESXi-centric campaigns, particularly targeting hypervisors in retail environments |
| ESXiArgs | Ransomware | Purpose-built ESXi ransomware responsible for widespread global compromises |
| Akira | Ransomware | Active since 2023; uses specialized ESXi encryptors and exploits vulnerabilities for mass encryption |
| Black Basta | Ransomware | Targets ESXi using multi-threaded ChaCha20 to maximize encryption speed across multi-CPU hosts |
| Cactus | Ransomware | Integrated ESXi-specific targeting into operations as of late 2024 |
| Play | Ransomware | Uses Linux-based lockers designed to encrypt virtual machine files on ESXi hosts |
| DarkBit | Ransomware | Uses stealthy access methods, including SSH tunneling, to compromise and encrypt hypervisors |
| Conti | Ransomware | Early adopter of Linux/ESXi lockers; tooling and code later reused across multiple groups |
| Hive | Ransomware | Developed ransomware variants for Linux, VMware ESXi, and FreeBSD |
| Bert | Ransomware | Includes an ESXi-compatible encryptor that supports multi-threaded encryption and virtual machine shutdown to maximize host-level impact |
| Scattered Spider | Ransomware / Intrusion | Focuses on cloud and virtualized environments, including ESXi, often preceding ransomware deployment |
| PRC – BRICKSTORM (UNC5221) | Nation-State Espionage | VMware vSphere backdoor designed for long-term persistence and covert intelligence collection |
| PRC – “Fire Ant” (UNC3886) | Nation-State Espionage | Specializes in hypervisor-to-guest lateral movement within virtualized environments |
Defense Strategies
Configuring ESXi Log Forwarding
Broadcom provides built-in capabilities to forward ESXi syslog data to a centralized logging platform (SIEM). Centralized log forwarding enables monitoring of authentication events, configuration changes, shell activity, and other host-level operations.
Before configuration:
- Verify the vCenter instance managing the ESXi host is registered.
- Confirm you have sufficient privileges to modify HostConfiguration → Advanced settings and Security profile and firewall.
- Ensure permissions are set at the appropriate inventory level with Propagate to children enabled.
- Avoid running parallel configuration tasks, as this may result in incorrect syslog settings.
Configure Log Forwarding via vSphere
- Navigate to Integration → vSphere.
- Locate the instance managing the target ESXi host and select Edit.
- Select Configure ESXi hosts to send logs to Operations for Logs.
- By default, ESXi hosts version 5.5 and later are configured to forward logs via UDP.
- To modify protocol or scope:
- Select Advanced Options.
- Choose to configure all hosts or specific hosts.
- Select the desired syslog protocol.
- If using SSL, download the certificate and add it to each ESXi host’s certificate store.
- If using clusters, specify the hostname or IP address of the load balancer distributing syslog feeds.
- Click Save and verify configuration status under the ESXi hosts configured column.
Centralized log forwarding is required to detect many of the behaviors described below. Without remote ingestion, critical host-level activity may not be visible outside the ESXi console.
Core ESXi Logs and What They Reveal
Understanding which logs record specific actions enables more focused and effective detection.
- Shell Logs record commands executed directly on the ESXi host, including esxcli activity. These are key for spotting hands-on-keyboard actions and unauthorized configuration changes.
- Hostd Logs capture host management activity such as authentication events, VM lifecycle actions, and administrative changes made through vSphere clients or APIs.
- VMK Warning Logs surface kernel warning-level events, making them useful for detecting misconfigurations, time manipulation, or early signs of system abuse without parsing full kernel logs.
- ESXi Update Logs track patching and VIB installations and are critical for identifying unsigned or unauthorized updates that could indicate persistence or tampering.
Threat Hunting / Detection Opportunities from Available ESXi Logging
As with any logging and monitoring capability, the effectiveness of hunting and detection for these behaviors depends on how often similar activity occurs as part of normal business operations. We encourage organizations to hunt for each behavior and understand the expected baseline of your specific environment before trying to establish alerting.
| Behavior Name | Detection Logic | Significance | MITRE Technique |
| VM Snapshots Deleted | message contains “Removeallsnapshots received” | Destroys recovery capability before ransomware deployment. Highly indicative of imminent attack. | T1485 |
| Firewall Disabled | message contains “Firewall has been disabled” | Removes network protection, enables lateral movement and data exfiltration. | T1562.004 |
| User Granted Admin Role | message contains “esxcli system permission set” AND “role Admin” | Creates unauthorized privileged access for persistence. | T1078 |
| SSH Access Enabled | message has_any ( “Accepted keyboard-interactive”, “vob.user.ssh.session.opened”, “SSH session was opened”, “/rest/appliance/access/ssh”, “SSH access has been enabled”) |
Common first step for remote access and persistence after initial compromise. | T1021.004 |
| External Root Login | message contains “root” AND “logged in” | Direct root access to external authentication indicates potential credential compromise. | T1078 |
| Syslog Configuration Changed | message contains “syslog config set” OR “Syslog.global.logHost” | Disables logging to evade detection and hinder forensics. | T1562.001 |
| VM Autostart Disabled | message contains “AutoStartManager” AND “reconfigure” | Prevents recovery after system reboot – common ransomware tactic. | T1529 |
| Encryption Settings Modified | message contains “system settings encryption set” and message contains ” -s ” and message contains ” -e ” and message has “–require-secure-boot” and message contains “require-exec-installed-only” and message contains “execInstalledOnly” | Detects the disabling of critical encryption enforcement settings on an ESXi host. | T1562.001 |
Hardening and Mitigation Recommendations
Vendor Specific
Broadcom (VMware vendor) provides extensive security guidance for ESXi environments, key recommendations include:
- Keep ESXi Shell and SSH disabled by default: Only enable these privileged interfaces temporarily for troubleshooting, then disable immediately after use.
- Never manage ESXi hosts directly: Always administer through vCenter Server using vSphere Client rather than direct access via VMware Host Client or Direct Console User Interface (DCUI).
- Maintain minimal attack surface: Keep all non-essential ports closed and services disabled, only opening additional firewall ports when explicitly required.
- Enable hardware-rooted security features: Use UEFI Secure Boot and TPM 2.0 together to prevent unsigned code execution and establish hardware-based trust.
- Use only VMware sources to upgrade ESXi components: Never use third-party patches or downloads for ESXi components as they may compromise security or functionality.
Additional Recommendations
- Enhanced Visibility: Establish continuous log forwarding from ESXi and vCenter infrastructure to a SIEM environment with purpose-built detection rules targeting hypervisor-layer compromise indicators.
- Decouple Critical Dependencies: Sever direct ESXi host integration with Active Directory to shrink the AD attack surface.
- Modernize Authentication: Deploy phishing-resistant multi-factor authentication for vCenter.
- Network Segregation: Segregate the hypervisor’s management network from production and general user networks. Create a dedicated VLAN or network segment that is logically and/or physically separate. Limiting the number of endpoints that can attempt to connect to the hypervisor management interface drastically reduces the potential attack surface.
- Patch Management & Inventory: Maintain inventory of all ESXi hosts, vCenter, and associated management components with current patch levels.
Prioritize security patches and updates, especially for hypervisor-related CVEs and subscribe to VMware Security Advisories and Security Alerts mailing list.
Conclusion
Recent ransomware campaigns and nation state activity reinforce that hypervisor compromise is an established attack path with severe operational consequences. Defending ESXi environments requires treating the hypervisor as critical infrastructure rather than supporting technology. Organizations that prioritize patching, minimize direct access, harden identity and network boundaries, and actively monitor native ESXi logs will be far better positioned to detect early warning signs and disrupt attacks before they escalate into full scale outages.
SRA used extensive research into ESXi threats and created an actionable, live purple team test plan. To learn more about how to use the ESXi purple team to assess your organization’s preparedness for ESXi attacks, contact us at the form below.






