Call center operations are not immune to changing compliance requirements even though addressing compliance needs is not their primary function. The Payment Card Industry Security Standards Council (PCI SSC) has introduced additional guidance on securing cardholder data transmitted via VoIP. Call centers and organizations accepting credit card payments over the phone are most likely to be affected by this change and may not be adequately prepared to incorporate the new guidance. Below we will review the key components and potential design solutions to minimize scope and risk to your PCI environment.
How have the call centers attained PCI compliance in the past?
Telephony systems at call centers have traditionally been omitted from scope as the risk of man-in-the-middle attacks to compromise telephone-based credit card transmissions is considered to be generally low.
Many call center processes require customers to verbally provide payment information to call center agents; agents then enter payment information into a secure credit card terminal. ‘Pause and resume’ functions can be added to quality assurance platforms to restrict recording customer payment information. Historically, the combination of secure card readers and “pause and resume” was enough for organizations to claim PCI compliance, though they only resolve one part of the problem – eliminating the user workstation from scope.
The pause and resume feature prevents the storage of sensitive data within call recordings, but it does not address the underlying telephony systems and the VoIP infrastructure on which the credit card number is transmitted within the environment. The VoIP infrastructure is the second crucial part of the compliance equation and is still considered in-scope for the organization’s Cardholder Data Environment (CDE) as per the enhanced PCI SSC guidance.
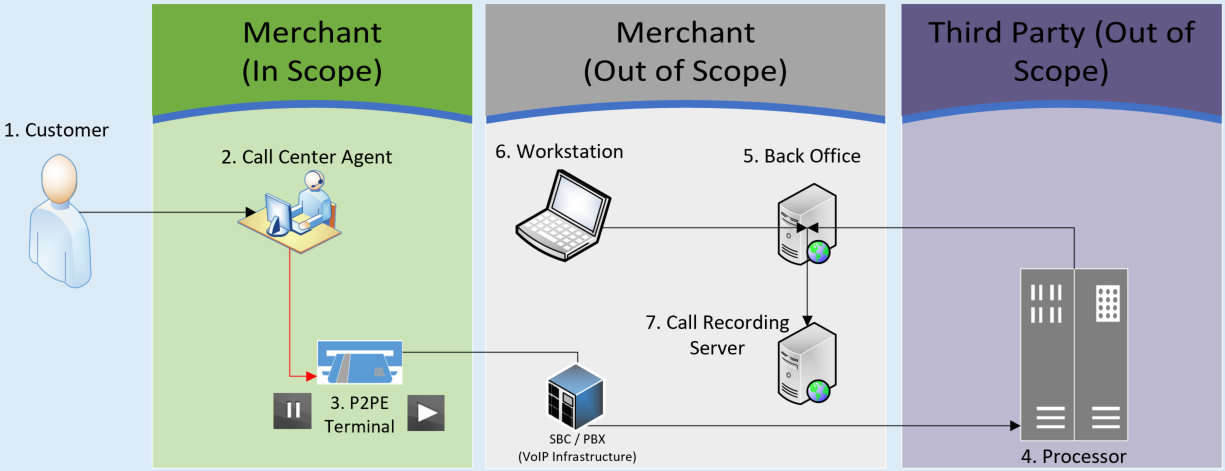
Figure 1 – Legacy Scope & Processes
What additional guidance has the PCI SSC provided?
The PCI Council released the Information Supplement: Protecting Telephone-Based Payment Card Data in November 2018 to reiterate that PCI scope applies to VoIP processes and to provide additional guidance for securing telephone systems. Any voice traffic from the carrier network that terminates on the equipment owned or operated by the entity and sent to a payment processor – irrespective of analog, digital, or VoIP transmission – should be considered in-scope for PCI DSS. Additionally, any telecommunication equipment owned and operated by a third-party, but hosted within the entity’s infrastructure for the purpose of provisioning access to a public network should also be considered in scope for PCI DSS. Guidance from the PCI SSC highlights that Requirement 4.1 applies wherever account data is transmitted over a shared or public VoIP service; additional details on the call center compliance guidance can be obtained here.
What solutions can you implement to achieve PCI compliance?
DTMF (Dual Tone Multi-Frequency) Suppression or Muting
DTMF is a technology in which voice-frequency band over telephone lines is used by the agents to securely collect payment information and process transactions. With DTMF masking, a customer enters the credit card information into their own telephone handset instead of reading it aloud to the agent. During this process, data is intercepted by the solution sitting upstream of merchant’s telephony environment and the agent cannot hear or see the full credit card digits on their screen. Credit card details are masked on the agents screen and sent to merchant’s processors via a secure medium to complete the transaction. This technology addresses both parts of the compliance equation: it removes the call center agent workstations and VoIP infrastructure from PCI scope. Existing call recording functions can continue in the background and agents can stay on the line with customers when they are entering the card details.
How it Works:
DTMF muting solutions can be either deployed on-premise or in the cloud depending upon the business and compliance needs. Regardless of deployment model, the DTMF solution sits upstream of the merchant’s telephony environment and in-scope call paths (inbound and outbound) are first routed to the DTMF environment via the merchant’s carrier provider. The DTMF provider validates the entered cardholder details and removes credit card information with flat frequency tones; clean data (non-PCI) is then passed to the merchant’s environment via the carrier provider to complete the transaction. This process ensures that cardholder data is not stored, processed, or transmitted through the merchant environment.
Mitigated Scope and Risks:
DTMF solutions reduce the PCI footprint for the merchants as VoIP infrastructure (e.g., session boarder controller (SBC) and private branch exchange (PBX) servers) does not process and / or transmit cardholder data over voice or data connections.
Cloud deployment is a seamless model and may provide additional scope reduction benefits, namely in minimizing responsibilities to manage underlying infrastructure – system hardening, patch management, vulnerability scanning, logging & monitoring. If the solution is deployed on-premise, additional controls may be applicable including physical security and network configuration controls as infrastructure is hosted within the merchant’s environment. Overall, the complexity and dependencies in telephony processes require coordination from many teams including business units, telecom, carrier providers, payment service providers, and even QSAs to effectively deploy the solution and attain maximum compliance and security benefits.
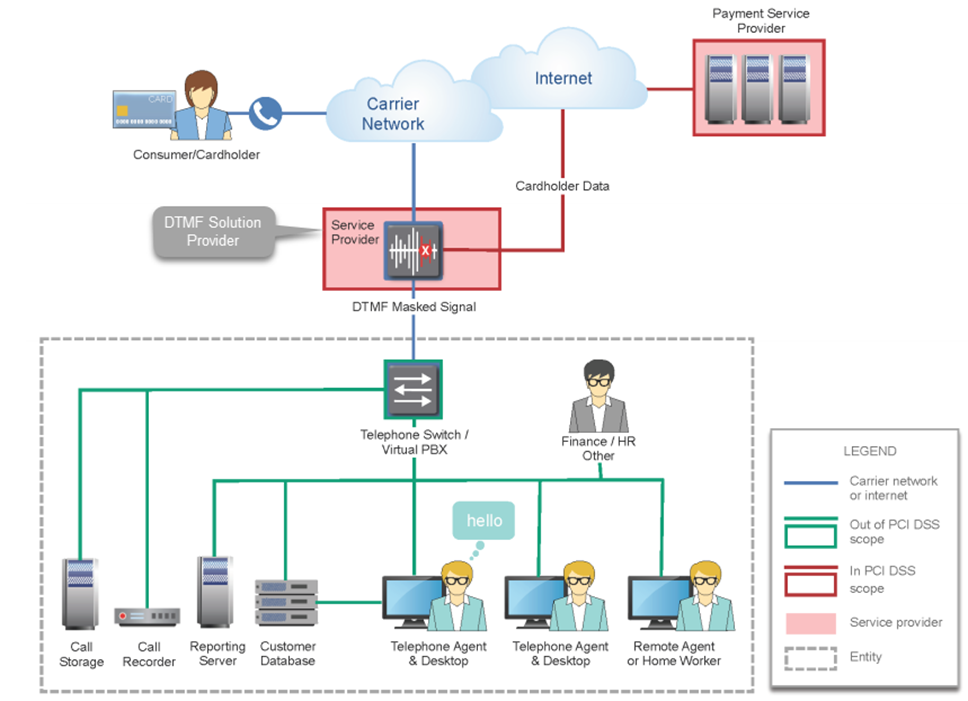
Figure 2 – Off-premise deployment of DTMF muting [1]
Outsourced Call Center Operations
Organizations can outsource the handling and processing of cardholder data to a PCI compliant service provider to reduce the liability to your organization and de-scope customer service processes and systems from the PCI environment. It is imperative to evaluate both ongoing operational costs and impact to the customer experience when outsourcing call center functions.
Merchants outsourcing call center operations may be able to attest to significantly fewer PCI DSS controls. SRA recommends engaging technical stakeholders including network and telecom teams to understand the impacts of proposed implementations.
P2PE + Pause & Resume + Network Isolation
Based on existing processes and the complexity of the environment, organizations may opt for a combination of solutions; however, there may be a significant lift to stand up an isolated environment for PCI systems.
For example, network re-architecture would be required to separate PCI systems (VoIP infrastructure, PBX servers, etc.) from the remainder of the corporate network to limit scope creep. P2PE credit card terminals would be used to eliminate workstations from the PCI scope and a pause and resume feature must be activated while collecting payment information to restrict the storage of cardholder data. Migrating servers, reviewing configurations, testing connectivity, and deploying new hardware all require additional resources to build out, secure, and maintain a dedicated PCI environment.
Information security practices (e.g., anti-virus/ anti-malware, vulnerability scanning, logging and monitoring) also come into scope in this scenario. Ongoing maintenance and support required to maintain this solution in a Business-as-usual (BAU) state is significant and requires inputs from multiple teams.
The following table compares features across the solutions mentioned above:
| Criteria | DTMF Muting | Outsourced Call Center Operations | P2PE + Pause & Resume + Network Isolation |
|---|---|---|---|
| Implementation Efforts | Medium | Low | High |
| Initial Costs (CapEx / OpEx) | High | High | Medium |
| Ongoing Costs (CapEx / OpEx) | Low | Medium | Medium |
| Ongoing Maintenance | Low | Low | High |
| Compliance Efforts | Low | Low | High |
| Residual Risk | Low | Medium | Medium |
| Impact to Customer Exp. | Low | Medum | Medium |
| Applicable Future State SAQ | SAQ A* | SAQ A | SAQ C |
*Note: DTMF solutions can be deployed in multiple models (cloud, on-prem, or hybrid) depending upon the vendor. Environments using DTMF may not be eligible for SAQ A in all scenarios but it is the best-case possibility.
All of the aforementioned solutions will enable you to reduce PCI scope, risk, and move towards PCI compliance but with varying degrees of effort and cost. DTMF muting solutions provide the highest security capabilities among the available options to safeguard CHD and reduce the compliance burden to maintain your PCI compliance status.
References
[1] Protecting Telephone-Based Payments Special Interest Group, PCI Security Standards Council, Information Supplement: Protecting Telephone-Based Payment Card Data, Diagram 7, pg. 38
Deep Haria
Deep has experience conducting audits and information security gap assessments against industry standards including PCI DSS, HIPAA, NIST, and other tools. He has also performed scope reduction assessments to help clients reduce their PCI compliance liability.
Deep has worked with clients in many industries including retail, technology, healthcare, and pharmaceuticals.
Deep has expertise with the GRC tool RSA Archer and helped clients develop application workspaces and on-demand enhancements. He is an RSA Archer Certified Professional and a PCI Professional in addition to being proficient in 5 languages.
Deep graduated from Pennsylvania State University, Berks with a major in Information Science Technology.





