Summary
SRA TIGR research has exposed a wave of SMS-based phishing (smishing) campaigns that is actively targeting organizations across multiple sectors using compensation-themed lures to harvest credentials. Technical analysis of the phishing infrastructure ties the activity to EvilProxy, an Adversary-in-the-Middle (AiTM) phishing toolkit sold as a service on dark web marketplaces. The backend hosting infrastructure is consistently linked to Cloudzy (operating as RouterHosting LLC), a Virtual Private Server (VPS) provider that has been publicly documented as a front for abrNOC, an Iranian company headquartered in Tehran.
While evidence supports infrastructure overlap and tradecraft consistency, definitive attribution of this specific campaign to an Iranian state actor cannot be made. Still, multiple independent research efforts have documented the same Cloudzy/RouterHosting infrastructure being used to support nation-state espionage operations, ransomware affiliates, and other criminal activity. With this in mind, organizations should block traffic to and from Cloudzy/RouterHosting network ranges where no legitimate business need exists and review their defenses against AiTM phishing techniques.
What Is EvilProxy?
EvilProxy is an Adversary-in-the-Middle (AiTM) phishing toolkit that specializes in bypassing Multi-Factor Authentication (MFA) through real-time session harvesting. Rather than simply stealing a username and password, EvilProxy sits as a reverse proxy between the victim and the legitimate service being impersonated. The platform operates as a commercial service with subscription-based offerings.
How the attack works:
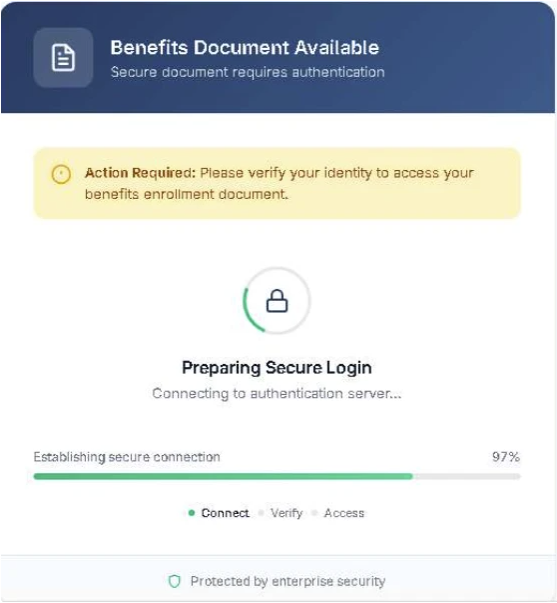
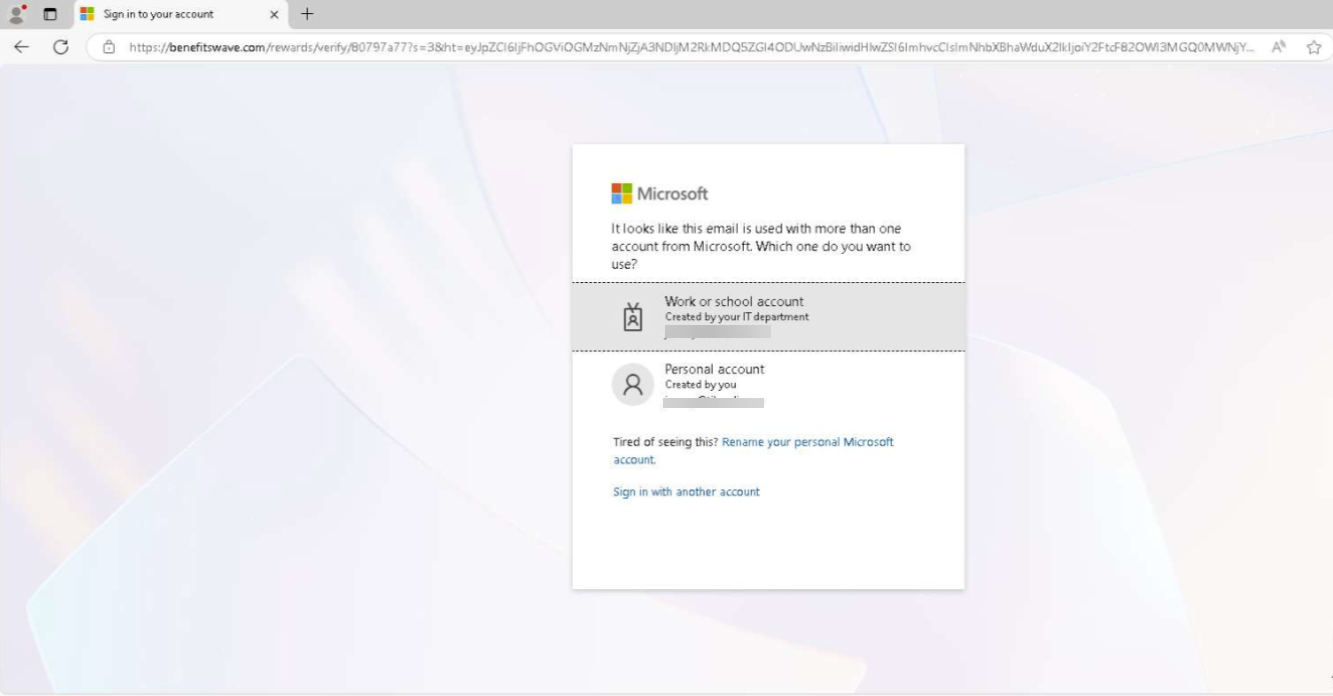
- The victim receives a smishing message with a malicious link and clicks through to what appears to be a legitimate login page.
- EvilProxy proxies the authentication request to the real service in real time, relaying credentials and MFA prompts transparently so the login appears to succeed normally.
- As the victim completes MFA, EvilProxy captures the resulting authenticated session cookie — the token that proves the login was successful.
- The attacker then uses that harvested session cookie to access the victim’s account directly, bypassing the need for credentials or MFA entirely, as the session is already authenticated.
Cloudzy/RouterHosting Connections to Iran
The hosting infrastructure behind the observed campaign is tied to Cloudzy, a VPS provider that markets anonymous hosting services and accepts cryptocurrency payments including Bitcoin, Monero, and Zcash. Cloudzy operates under the U.S.-registered entity RouterHosting LLC, which was incorporated in Sheridan, Wyoming, but was dissolved in 2024.
In August 2023, anti-ransomware firm Halcyon published a detailed investigation titled Cloudzy with a Chance of Ransomware that assessed with high confidence that Cloudzy is a front for abrNOC, an Iranian hosting company headquartered on Fatemi Square in Tehran. The two companies share nearly identical logos, claim the same 15+ data center locations, were both founded in 2008, and are led by the same individual, Hannan Nozari. Halcyon identified eight Cloudzy employees in Iran who showed direct crossover with abrNOC staff, and found that some Cloudzy employee profiles appeared to be fictitious. Halcyon estimated that 40-60% of all activity on Cloudzy infrastructure was malicious in nature.
In March 2026, Flare published research documenting a separate, concurrent phishing operation hosted on RouterHosting/Cloudzy that targeted Canadian residents. That campaign used fraudulent domains impersonating the Government of British Columbia and Hydro-Quebec to collect personal information and credit card details. Flare identified 134 Canadian-specific (.ca) domains on RouterHosting’s network, 58% of which contained language assessed as suspicious, referencing banks, utility providers, or payment-related terms. The naming conventions suggested the operation may extend beyond Canada to target residents of other countries as well.

The significance of Cloudzy/RouterHosting infrastructure extends well beyond the current phishing campaigns. Halcyon’s 2023 report documented that the provider’s network has been used by threat actors spanning at least seven nations. The full roster of groups identified on Cloudzy infrastructure includes some of the most prolific operators in both state-sponsored espionage and financially motivated cybercrime.
Threat Actors with Historical Connections to This Infrastructure
| Cluster / Function | Threat Groups | Overlap (Tradecraft / Role) | Details & Context |
| Iranian State Espionage & Pre-Positioning | APT34 (OilRig), MuddyWater, APT35 (Charming Kitten) | Credential harvesting, phishing, LOTL (PowerShell), infrastructure staging | MOIS/IRGC-linked groups focused on long-term access, surveillance, and pre-operational footholds. Frequently reuse infrastructure and staging environments prior to follow-on activity. |
| Iranian Disruption, Influence & Hacktivism Layer | APT33, Cotton Sandstorm, CyberAv3ngers, Handala | Wipers, disruptive ops, hack-and-leak, ICS targeting | Blend of state-directed and proxy/hacktivist actors used for disruptive signaling, influence campaigns, and critical infrastructure targeting. Often surge during geopolitical escalation. |
| Russian State Espionage | Nobelium (APT29), Turla | Stealth persistence, supply chain compromise, long-term C2 | Advanced intelligence collection actors (SVR/FSB-linked) focused on government and enterprise espionage with highly covert tradecraft. |
| Russian Financially Motivated Operations | FIN12, Evil Corp | Ransomware, financial malware, rapid monetization | Criminal groups with high operational tempo; frequently target healthcare and financial sectors. Some overlap with state tolerance or indirect alignment. |
| China State Supply Chain & Espionage | APT10 (Stone Panda), | Supply chain compromise, MSP targeting, infrastructure development | Focus on scalable access through third parties and long-term intelligence collection. Heavy emphasis on global enterprise and service provider compromise. |
| North Korean Intelligence & Financial Operations | Kimsuky, BlueNoroff | Phishing, credential theft, financial exploitation (crypto) | Dual-mission operations combining espionage with revenue generation to support state objectives. |
| South / Southeast Asian Regional Espionage Cluster | Sidewinder, Bitter, Transparent Tribe (APT36), APT32 (OceanLotus) | Spear-phishing, regional surveillance, government targeting | Regionally focused actors conducting persistent espionage against neighboring states, defense sectors, and political entities. |
| Ransomware Ecosystem (Operators + Malware) | Ryuk, BlackCat (ALPHV), Ghost Clown | Ransomware deployment, double extortion, affiliate models | Interconnected ecosystem where operators shift between strains; access often brokered or reused across campaigns. |
| Initial Access & Malware Delivery Layer | TrickBot, Space Kook | Initial access, loaders, lateral movement, ransomware staging | Provides footholds for ransomware or espionage actors; overlaps heavily with financially motivated campaigns. |
| Commercial Surveillance / Dual-Use Capability | Candiru | Spyware, surveillance tooling, exploitation-as-a-service | Commercial vendor providing capabilities used in state-aligned surveillance operations against civil society targets. |
Recommendations & Takeaways
The campaigns detailed above are not isolated incidents. They reflect a pattern of persistent, professionally maintained infrastructure with documented ties to Iranian threat actors and a broad range of criminal operators. Cloudzy’s bulletproof hosting environment makes this activity difficult to disrupt at the source, placing greater weight on defensive controls at the organizational level.
Defense Recommendations include the following:
- Reinforce training on SMS based phishing (especially messages referencing compensation, benefits, or HR matters) and consider performing smishing simulations to understand the posture of your workforce.
- Report any received smishing messages to your security team
- Block Cloudzy / ROUTERHOSTING IP ranges (144.172.x.x, 45.59.x.x, 172.86.x.x, 45.61.x.x, 216.126.x.x).
- Enforce phishing-resistant MFA (FIDO2/hardware security keys) where possible.
- Given the broader Iranian APT threat elevation, reinforce general phishing awareness for employees across email, SMS, and collaboration platforms (Teams, Slack).
- For deeper technical guidance on mitigating these exact threats, we recommend reviewing the recently published Security Risk Advisors (SRA) blog, “Defending and Hunting AiTM Attacks,” which details further defense and detection strategies.
| Type | Indicator | Context/Source |
| Domain | Tracking[.]kvo1[.]io | Direct redirector from the SMS lure. |
| Domain | kvo1[.]io | Direct redirector from the SMS lure. |
| Domain | rcl[.]ink | Direct redirector from the SMS lure. |
| Domain | Fastx[.]to | Identified in Any.run as associated with EvilProxy. |
| Domain | Benefitswave[.]com | Community-reported phishing domain. |
| IP Address | 172.86.105.195 | Associated Cloudzy (ROUTERHOSTING) node. |
| IP Address | 144.172.89.223 | Associated Cloudzy (ROUTERHOSTING) node. |
| Phone Number | 855 – 744 – 0142 | Source number of the initial SMS phishing (smishing) lure delivering the malicious redirector link. |
Sources
- Iran-Run ISP ‘Cloudzy’ Caught Supporting Nation-State APTs, Cybercrime Hacking Groups
- Phishing Campaign with Alleged Links to Iranian State Aligned Activity – Flare
- Iran Readied Cyberattack Capabilities for Response Prior to Epic Fury
- ASTRA RCE on Twitter / X
- Malware analysis https://tracking.kvo1.io/enSVbg Malicious activity | ANY.RUN – Malware Sandbox Online
- Malware analysis https://tracking.kvo1.io/uHfVbF Malicious activity | ANY.RUN – Malware Sandbox Online
- Interactive Online Malware Analysis Sandbox – ANY.RUN
- Automated Malware Analysis Report for https://tracking.kvo1.io/YeP5bW – Generated by Joe Sandbox
- Halcyon Cloudzy Report
- Amazon threat intelligence teams identify Interlock ransomware campaign targeting enterprise firewalls | Amazon Web Services
- Multiple Russian Threat Actors Targeting Microsoft Device Code Authentication
- North Korean Threat Actors Deploy Hidden Risk Malware on macOS to Target Crypto Firms – Active IOCs – Rewterz
- Iranian Cybercriminals Establish New Network to Attack US Political Campaigns – Active IOCs – Rewterz
- 5-Minute Hunt: Six Queries to Detect Iranian APT Activity by Lucie Cardiet
- A Practical Guide to Uncovering Malicious Infrastructure With Hunt.io
- ThreatsDay Bulletin: OAuth Trap, EDR Killer, Signal Phishing, Zombie ZIP, AI Platform Hack & More







